- Company
- Services
- Web Design Services
- Mobile Application Development
- Open Source Development
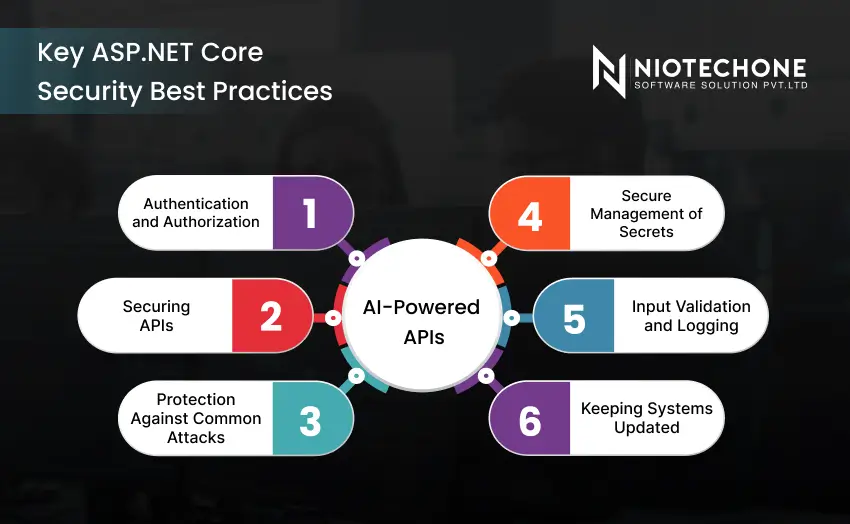
- Microsoft Application Development
- JavaScript Development
- Hire US
- IT Consulting
- Content Management System
- Custom Software Development
- Software Consulting Services
- Software Development Company
- Software Product Development
- Enterprise Software Development
- Custom Software Development
- All Services
- Expertise
- Hire Developers
- Hire Android App Developers
- Hire Angular JS Developers
- Hire ASP.Net Core Developers
- Hire ASP.NET Developers
- Hire Codeigniter Developers
- Hire Dedicated NodeJS Developers
- Hire Drupal Developers
- Hire e-Commerce Developers
- Hire iPad App Developers
- Hire iPhone app Developers
- Hire Laravel Developers
- Hire Magento Developers
- Hire Php Developers
- Hire React Native Developers
- Hire ReactJS Developers
- Hire Web Designers
- Hire Web Developers
- Hire WordPress Developers
- Hire Windows App Developers
- Technologies
- Portfolio
- Careers
- Contact Us