Why Traditional App Security Is No Longer Enough
- Niotechone Marketing Team
Table of Contents
- Introduction
- What Traditional Application Security Generally Includes
- Why Traditional Security Models Fail in 2026
- The Rise of API-Centric and Mobile-First Applications
- The Major Threat is Now Identity-Based Attacks
- Why Security Should Be Architected, Not Applied
- AI has transformed Attacks and Defenses
- Comparison: Traditional Security vs Modern Application Security
- Real-World Case: Security Modernization in Action
- Secure Development Practices in 2026
- Why Businesses Collaborate with Security-Conscious Development Teams
- Conclusion: Security Should Change With Your Software
Introduction
Over the years, application security has focused on perimeter defense, basic authentication, and periodic security testing. Although these measures worked in the past, they no longer provide adequate protection for modern software systems. By 2026, companies will host applications in the cloud, build them around APIs, integrate them with third-party services, and connect them to AI-driven automation. This expansion increases the attack surface and makes traditional security models obsolete.
The threats to business owners, CTOs, and enterprise leaders now stem from architectural vulnerabilities, improperly configured cloud environments, open APIs, and identity layers, rather than from application code. A modern custom software development company should consider security as an architectural, ongoing issue, not a checklist item. This article describes why conventional app security is no longer effective and what modern enterprises should do instead.
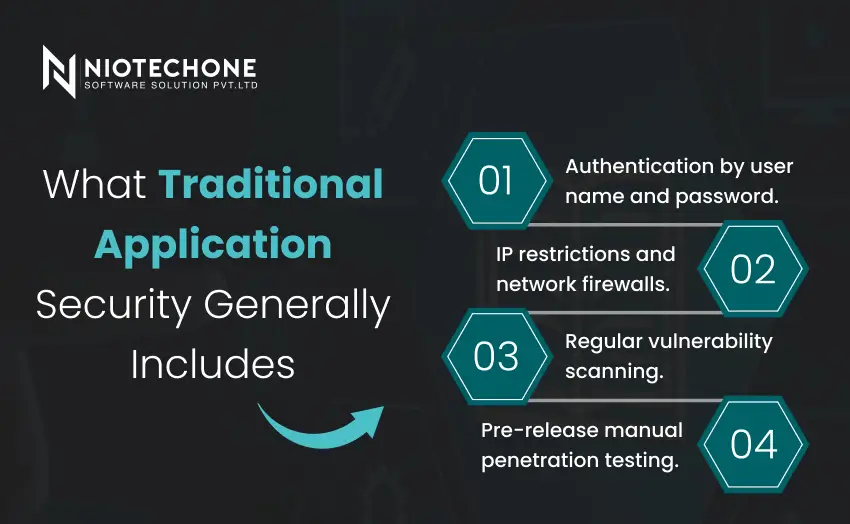
What Traditional Application Security Generally Includes
Conventional security strategies supported simpler systems with minimal exposure. They generally focus on:
Teams authenticate users with usernames and passwords.
Administrators enforce IP restrictions and configure network firewalls.
Security teams conduct regular vulnerability scans.
Experts perform manual penetration testing before release.
These approaches assume that applications remain mostly static, operate in controlled environments, and receive infrequent updates. Modern scalable software applications no longer follow this pattern.

Why Traditional Security Models Fail in 2026
1) The Attack Surface Has Gone Beyond the Application
Modern applications are based on APIs, cloud services, third-party integrations, mobile clients, and external identity providers. All the components present possible vulnerabilities that traditional security models do not completely cover.
One open API endpoint or improperly configured cloud resource can bring down the whole system, despite the underlying application code being secure.
2) Cloud-Native Architecture Changes Security Responsibility
Security in cloud application development is no longer the responsibility of infrastructure teams. Although the platform is secured by cloud providers, application owners are in charge of:
- Identity and access control.
- API security
- Data encryption
- Configuration hardening
Applications developed on the Azure cloud architecture are susceptible to attacks without a cloud-aware security design, even when they are deployed on enterprise-grade infrastructure.
The Rise of API-Centric and Mobile-First Applications
Modern applications rely on APIs by default.
APIs create high-risk targets for several reasons. APIs often:
Expose business logic.
Process sensitive data transactions.
Handle high concurrency.
Most breaches do not occur because APIs exist; they happen because teams fail to implement proper authorization, rate limiting, or input validation. A skilled ASP.NET Core API development company builds APIs with security controls embedded at the architectural level.
The Major Threat is Now Identity-Based Attacks
In 2026, attackers do not often hack applications directly. They instead take advantage of identity weaknesses.
Ordinary Identity Security Failures.
- Over-privileged user roles
- Lax token expiration policies.
- Lack of consistency in authorization logic.
- Poor session management
The current ASP.NET Core application architecture focuses on identity-first security, where all requests are authenticated and authorized at all times.
Why Security Should Be Architected, Not Applied
Security added after development usually results in:
- Performance degradation
- Complex patching
- Incomplete coverage
Principles of Secure Architecture
A secure enterprise application consists of:
- Stateless service design
- Clear trust boundaries
- Single identity management.
- Secure API gateways
These are the principles that are fundamental to the development of enterprise .NET applications, particularly those likely to scale.
AI has transformed Attacks and Defenses
The way AI poses a greater security risk.
Attackers now use AI to:
- Automate vulnerability discovery.
- Initiate credential-stuffing attacks.
- Take advantage of misconfigurations at scale.
Conventional defences cannot react quickly to automated threats.
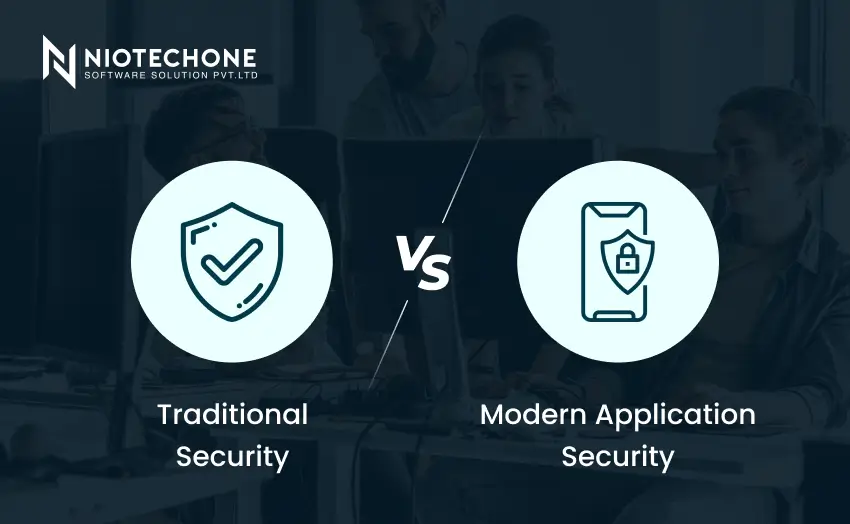
Comparison: Traditional Security vs Modern Application Security
Aspect | Traditional App Security | Modern App Security (2026) |
Focus | Perimeter defense | Identity & architecture |
Update Cycle | Periodic | Continuous |
Cloud Awareness | Limited | Native |
API Protection | Minimal | Centralized & enforced |
AI Integration | None | Active threat detection |
Scalability | Weak | Designed for growth |
Real-World Case: Security Modernization in Action
A medium-sized SaaS company was repeatedly abused by API even after undergoing regular security audits.
Initial Setup:
- Monolithic architecture
- Auth without scopes using tokens.
- Manual security reviews
Modernization Approach:
- Migrated to ASP.NET Core APIs
- Implemented centralized identity management.
- Added automated security surveillance.
Outcome:
- Reduction in security incidents by 60 percent.
- Faster incident detection
- Enhanced compliance preparedness.
Niotechone Software Solution Pvt. Ltd. led this transformation, which guaranteed security enhancements in line with business expansion.
Secure Development Practices in 2026
Security is no longer the property of one team.
Secure Development Now Requires:
- Secure coding standards
- Automated security testing
- Cloud configuration validation.
- Continuous monitoring
These practices are incorporated into the daily development processes by modern custom .NET development services.
Why Businesses Collaborate with Security-Conscious Development Teams
Most organizations do not have the internal skills to manage the complexity of security in the modern world. This is why they:
- Recruit security-experienced developers.
- Collaborate with expert software development companies.
- Aim for long-term security ownership, not one-time audits.
This continuity is offered by teams with experience in ASP.NET development and cloud-native security.
Conclusion: Security Should Change With Your Software
Conventional application security methods served a different era that had less exposure, simpler architectures, and slower release cycles. In 2026, applications operate in dynamic, distributed environments and integrate tightly with cloud platforms and APIs. Old security models expose businesses to risks that become difficult and expensive to recover from.
The current security demands an architectural thinking that focuses on identity, automation, and constant monitoring. Companies that invest in secure design early on mitigate long-term risk, enhance system resilience, and safeguard customer trust. By engaging a seasoned software development company such as Niotechone Software Solution Pvt. Ltd., you can be sure that security keeps pace with your application and does not drag it down.
Categories
Related Articles
Frequently Asked Questions FAQs
Since modern applications are based on APIs, cloud services, and distributed systems, traditional models were not built to be secure.
No. Azure provides platform security, but it is your duty to provide application-level security.
Yes, one of the most frequent entry points for attackers is poorly secured APIs.
AI allows real-time threat detection, anomaly monitoring, and automated response.
No. Security should be integrated into architecture and development processes at the very beginning.