Embedded Security with DevSecOps
- Niotechone Marketing Team
Table of Contents
- Introduction
- Embedded Security and DevSecOps: A New Foundation of Modern Engineering
- The Reason Why Security Should be Built into Product Design
- The Transformation of Embedded Development by DevSecOps
- Basic Building Blocks of an Embedded DevSecOps Pipeline
- The Intersection of Embedded Security and Cloud Ecosystems
- Embedded Security Problems and DevSecOps Solutions
- Best Practices to Implement Embedded DevSecOps
- Real-world Applications Where Embedded DevSecOps Make a Real Difference
- Embedded DevSecOps Business Benefits
- Conclusion
Introduction
The current digital ecosystems are not based on software only anymore, they are executed on embedded systems that drive IoT devices, medical equipment, automobiles, industrial robots, payment terminals, smart appliances, etc. The attack surface increases exponentially as these systems become highly interconnected. This is where embedded security DevSecOps comes in as not only useful, but also necessary.
In India, particularly in the case of teams such as a .NET development company in Rajkot, a software development company in Rajkot, and enterprise teams that provide custom software development or Azure cloud application development, secure embedded workflows have become a fundamental need in large-scale digital transformation.
Embedded Security and DevSecOps: A New Foundation of Modern Engineering
Traditional development considered security as a post-hoc measure – a check prior to deployment. However, embedded systems are used in real-world, high-risk environments where vulnerabilities can be critical.
DevSecOps changes this paradigm by turning security into an ongoing and in-built process.
Why it matters
- Embedded devices are frequently high-value targets because they frequently contain sensitive data.
- Firmware is hard to upgrade, and thus the vulnerabilities remain unless they are handled at an early stage.
- Devices communicate with cloud systems, and it is crucial to integrate them securely.
DevSecOps assists teams to design, develop, test, and release embedded systems with security as a fundamental component, rather than an add-on, which is an essential benefit to companies offering AI in Software Development in Rajkot, custom Enterprise mobility software solutions, or .NET Core application development.
The Reason Why Security Should be Built into Product Design
Embedded devices are often continuously running, even years, without direct user control. This requires a strong, long-life cycle security model.
The main reasons why security should be built-in:
- Physical exposure: Sensors, kiosks, and IoT nodes are simple to compromise.
- Connectivity risks: The more the networking, the more the attack vectors.
- Complexity of firmware: One vulnerability can destroy a whole ecosystem.
Indian businesses that have implemented connected systems, such as travel platforms created by a Travel portal software development company in Rajkot, enterprise apps created by a web development company in Rajkot, and others, are now using embedded components. Security should then begin at the very beginning of architecture design.
The Transformation of Embedded Development by DevSecOps
DevSecOps incorporates security practices into automation pipelines. In the case of embedded systems, the effect is enormous as it integrates firmware development, hardware testing, and cloud integrations.
Embedded device transformation:
- Early threat detection through automation.
- Secure code inspection and static analysis on every commit.
- Firmware Continuous integration, minimizing late-stage surprises.
- Monitoring that is connected to the cloud, particularly in the development of Azure cloud applications.
- Safe OTA (Over-The-Air) updates, secure deployment pipelines
DevSecOps combines development, security, and operations, which brings predictability, which is a significant benefit to embedded technology vendors.
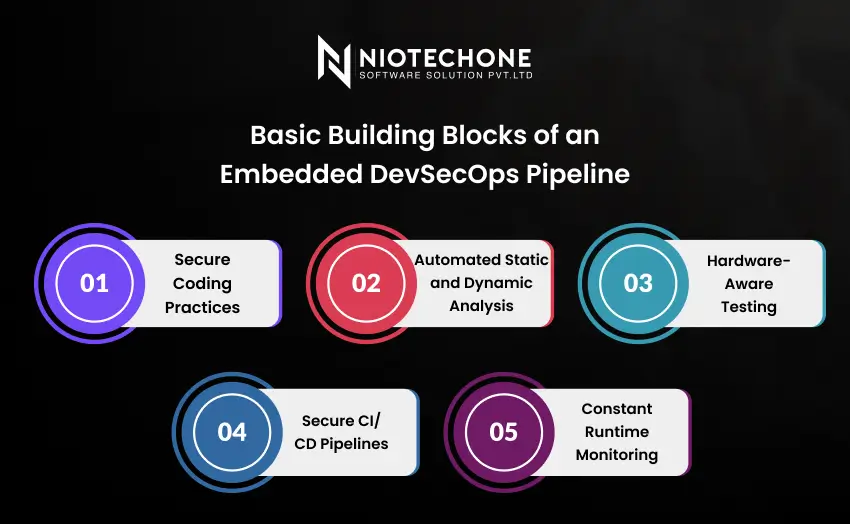
Basic Building Blocks of an Embedded DevSecOps Pipeline
An effective embedded DevSecOps workflow is a network of interdependent components that operate in perpetual harmony.
1. Secure Coding Practices
Encryption, memory safety, and validation are all strictly adhered to by developers.
2. Automated Static and Dynamic Analysis
Testing tools search risky patterns, weak dependencies, or firmware anomalies.
3. Hardware-Aware Testing
Simulators mimic the behavior of firmware and then flash actual devices.
4. Secure CI/CD Pipelines
Each firmware release is subjected to automated, regulated automation.
5. Constant Runtime Monitoring
Devices send anomalies to cloud platforms, which allows quick response.
All the components enable teams, such as ASP.NET Core development in Rajkot or embedded firmware development, to produce safer products.
The Intersection of Embedded Security and Cloud Ecosystems
Embedded security should go beyond the device as more and more modern devices are being integrated with cloud platforms such as Azure, AWS, and enterprise clouds.
Cloud-based embedded security brings:
- Cloud IAM identity management.
- Coded communication between devices and the cloud.
- Remote control of devices and secure OTA updates.
- Edge-cloud orchestration, enhancing the speed of decisions.
To engineering teams that provide Azure cloud application development or custom software development in India, this cloud-edge fusion presents both opportunity and responsibility – greater capabilities and greater security expectations.
Embedded Security Problems and DevSecOps Solutions
Embedded systems continue to encounter real-life challenges despite the progress.
Major challenges include:
- Protection is limited by the limited compute power of devices.
- Extended development cycles, particularly with industrial or medical equipment.
- Invisibility, which complicates the detection of runtime threats.
- Disjointed hardware ecosystems, which lead to integration complexity.
How DevSecOps Helps
- Security reviews are automated and identify problems at an early stage.
- Secure CI/CD speeds up firmware updates.
- Cloud monitoring enhances visibility.
- Integrated workflows minimize fragmentation.
Best Practices to Implement Embedded DevSecOps
Teams need to be organized in order to develop secure embedded systems.
Recommended practices:
- Left shift security: Begin at architecture, not development.
- Apply secure boot methods to avoid unauthorized loading of firmware.
- Use SBOM (Software Bill of Materials) to achieve supply-chain transparency.
- Secure communications between devices with current protocols.
- Require code-signing of all firmware updates.
- Even internal device-to-device communication should be run on zero-trust models.
These best practices are useful to organizations in India, particularly those that deal with enterprise mobility solutions, custom software development, or IoT-based platforms.
Real-world Applications Where Embedded DevSecOps Make a Real Difference
DevSecOps is changing embedded industries worldwide.
Key use cases:
- Intelligent medical devices that need safe patient information management.
- Autonomous cars that require real-time firmware protection.
- Automation in industries, where unsafe code can cause havoc in factories.
- Smart home gadgets, which can be attacked remotely.
- Travel and hospitality applications, particularly those developed by a Travel portal software development company in Rajkot, which are sensor-based data.
These illustrations demonstrate that embedded systems are dependent on contemporary DevSecOps to remain secure and dependable.
Embedded DevSecOps Business Benefits
Companies that adopt embedded DevSecOps have technical and business benefits.
Benefits include:
- Less vulnerability because of early detection.
- Reduced security fix cost, due to automation.
- Secure CI/CD with faster go-to-market cycles.
- Extended device lifecycle with secure OTA updates.
- Increased customer confidence through secure-by-design architecture.
- Better compliance, such as industry-specific regulations.
In the case of a software development company in Rajkot, a web development company in Rajkot, or a .NET development company in Rajkot, these advantages are directly related to the growth of the enterprise.
Conclusion
Security cannot be an option as embedded systems are the foundation of the new digital experiences. DevSecOps offers the framework, automation, and culture needed to create secure, dependable, and scalable embedded systems. Regardless of whether you build enterprise platforms, cloud solutions, AI-driven applications, or custom mobility systems, it is always the most intelligent decision to build security into it at the beginning. DevSecOps has ceased to be a trend and has become a necessity to organizations in India, particularly fast-growing teams such as web development companies in Rajkot and custom software companies. The future is in safe, independent, self-healing embedded ecosystems – and DevSecOps is the way to get there.
Categories
Related Articles
Frequently Asked Questions FAQs
Embedded security is the security of hardware-based systems (IoT devices, sensors, controllers, etc.) against unauthorized access, tampering, and cyberattacks.
It incorporates security checks during development and automates testing, which makes firmware more secure and updates quicker.
Yes, Despite the limitations of devices, the majority of security activities are performed within the CI/CD pipeline or cloud systems.
Software development company in Rajkot, providers of .NET Core applications development, and enterprise app developers have improved security, speed, and system reliability.
Code-signing systems, SBOM tools, cloud monitoring dashboards, and secure CI/CD pipelines.